About company
Taransvar is a Norwegian Non-Governmental Organization with a registered branch in Kenya (Taransvar CBO). We're dedicated to improving mental well-being through neuroscience, specifically by understanding neuroplasticity.
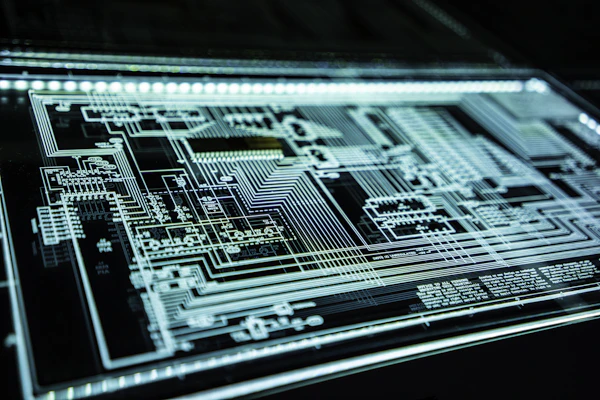
This research shows that mental challenges are essentially destructive "skills" that can be replaced by focusing on and developing better ones. By creating meaningful cybersecurity jobs, we provide precisely that – a constructive focus and a path to mental well-being.